WinLock Password Is Now Available To Help Protect And Hide Applications
The need to protect or hide your important documents especially when you wouldn’t use your PC for a quite a long period of time is a considerable and clever thing to do. Confidential documents or information needs the newly launched WinLock password. To access WinLock password, you must know the user account. Therefore, it is difficult for any person to access WinLock password without any idea of user account.
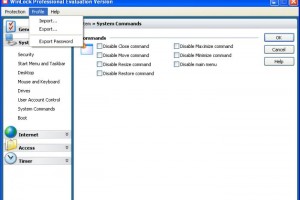
To create WinLock password just press and hold down Windows key then, press L key and everything is set. However, this idea is not applicable in a situation where the computer is shared regularly among many people. Instead, WinLock tool is required to hide and protect any of your programs in the computer. The WinLock password created on your application widow only denies any other user from accessing your information. The other user can use the computer freely but cannot reach your documents. The WinLock software only requires a capacity of 2.5MB RAM. It displays an icon to show its presence in the system. This program quietly runs in the background of the system. To avoid the casual inspection on the program, what you need to do is to alight on the icon then press Ctrl key together with Space key. The icon is moved to the system tray. However, in restoring the program you need to double click on the item icon then press in your WinLock password.
WinLock password protection consumes less space creating enough space for the rest of programs. It is bad when to if the work protected by WinLock was unsaved when the attacker might decide to break into this protection. Closing it manually, the program get locked which causes the closing of your unsaved documents. It is advisable to be sure on the application that you what to use WinLock password protection tool on. Select the program and then press Ctrl and Space keys. The importance of WinLock is that it allows you to protect an individual application by ensuring you confidentiality of your documents. This is a sufficient security to your application and passers-by cannot get any root to them.